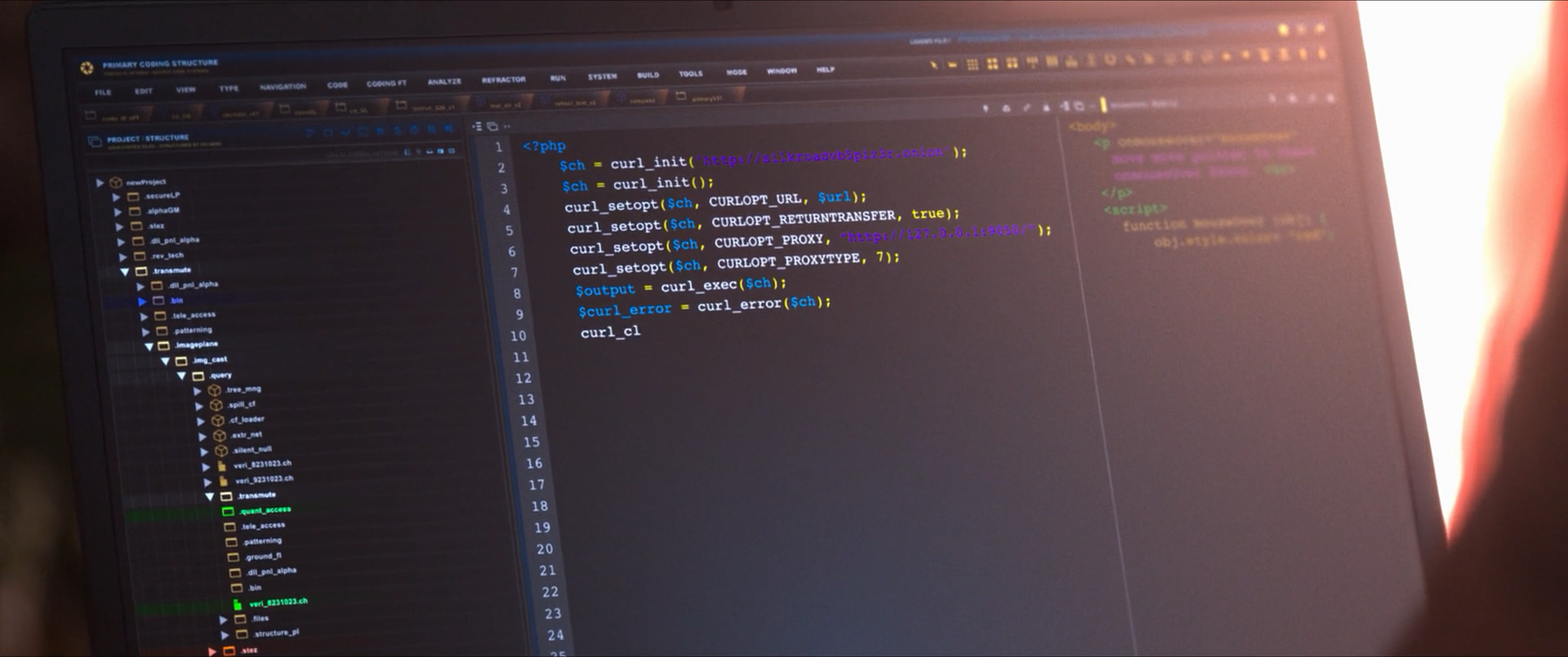
In the 2021 movie Silk Road, at around 19:23-19:26 into the film we can see Ross Ulbricht, the lead character, write a program on his laptop that uses curl. A few seconds we get a look at the screen as Ross types on the keyboard and explains to the female character who says I didn’t know you know how to code that he’s teaching himself to write code.
The code
Let’s take a look at the code on the screen. This is PHP code using the well known PHP/CURL binding. The URL on the screen on line two has really bad contrast, but I believe this is what it says:
<?php
$ch = curl_init("http://silkroadvb5pzir.onion");
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
curl_setopt($ch, CURLOPT_PROXY,
"http://127.0.0.1:9050/");
curl_setopt($ch, CURLOPT_PROXYTYPE, 7);
$output = curl_exec($ch);
$curl_error = curl_error($ch);
curl_cl
.onion is a TLD for websites on Tor so this seems legit as it a URL for this purpose could look like this. But then Ross confuses matters a little. He uses two curl_init() calls, one that sets a URL and then again a call without a URL. He could just have removed line three and four. This doesn’t prohibit the code from working, it just wouldn’t have passed a review.
The code then sets a proxy to use for the transfer, specified as an HTTP URL which is a little odd since the proxy type he then sets on the line below is 7, the number corresponding to CURLPROXY_SOCKS5_HOSTNAME – so not a HTTP proxy at all but a SOCKS5 proxy. The typical way you access Tor: as a SOCKS5 proxy to which you pass the host name, as opposed to resolving the host name locally.
The last line is incomplete but should ultimately be curl_close($ch); to close the handle after use.
All in all a seemingly credible piece of code, especially if we consider it as a work in progress code. The minor mistakes would be soon be fixed.
Credits
Viktor Szakats spotted this and sent me the screenshot above. Thanks!

The sad part about this is that one reason “frosty”, i.e. Ross Ulbricht, was caught was his post on stackoverflow:
https://stackoverflow.com/questions/15445285/how-can-i-connect-to-a-tor-hidden-service-using-curl-in-php
@Peter: Oh, I did not know about that. Thanks for this tidbit! Curious how similar that stackoverflow question’s code sample is to the code seen in the movie…