As I have been preparing slides for my coming talk at foss-north on April 28, 2026 I figured I could take the opportunity and share a glimpse of the current reality here on my blog. The high quality chaos era, as I call it.
No more AI slop
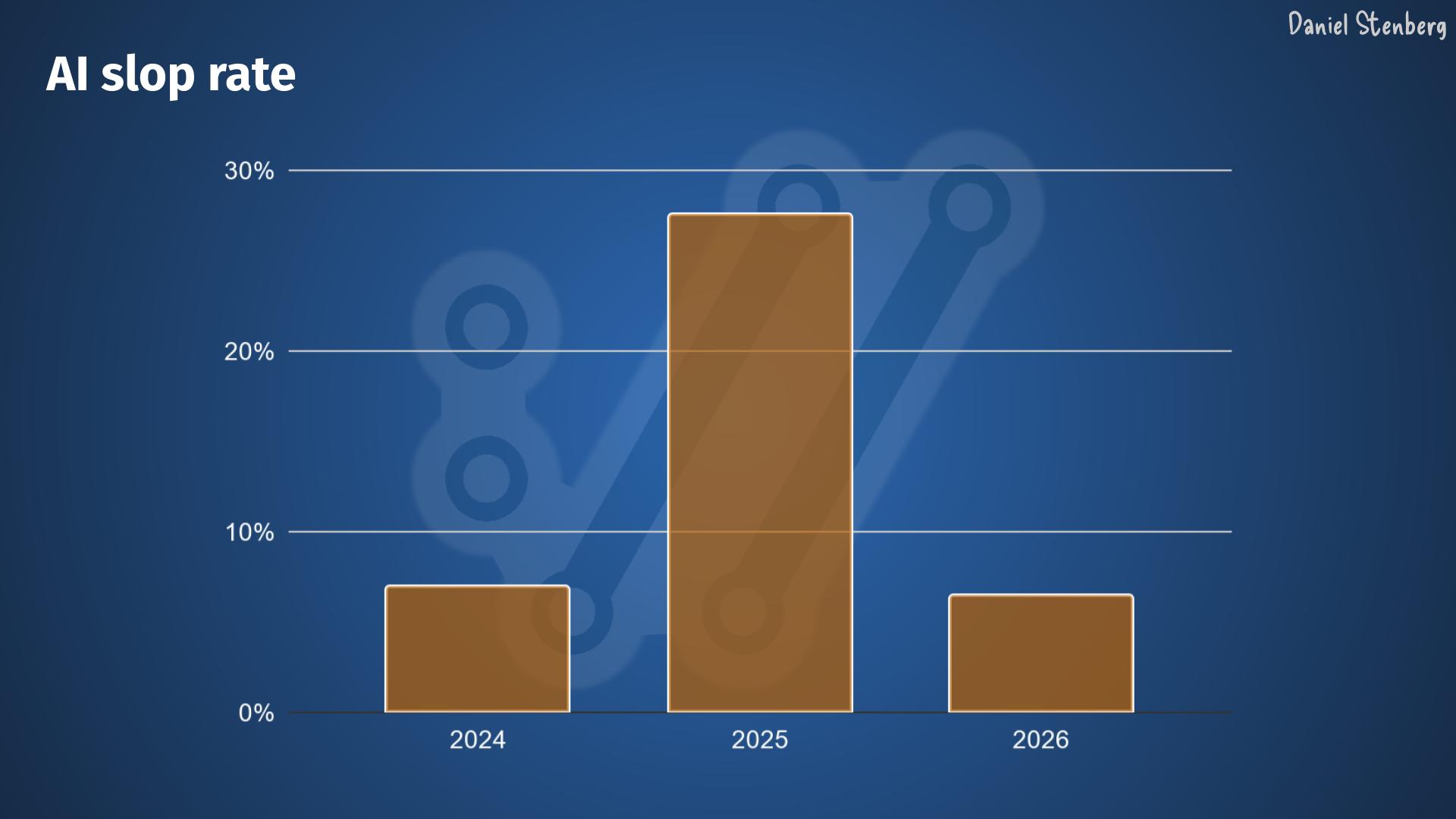
I complained and I complained about the high frequency junk submissions to the curl bug-bounty that grew really intense during 2025 and early 2026. To the degree that we shut it down completely on February 1st this year. At the time we speculated if that would be sufficient or if the flood would go on.
Now we know.
Higher volume, higher quality
In March 2026, the curl project went back to Hackerone again once we had figured out that GitHub was not good enough.
From that day, the nature of the security report submissions have changed.
The slop situation is not a problem anymore.
The report frequency is higher than ever. Recently it’s been about double the rate we had through 2025, which already was more than double from previous years.

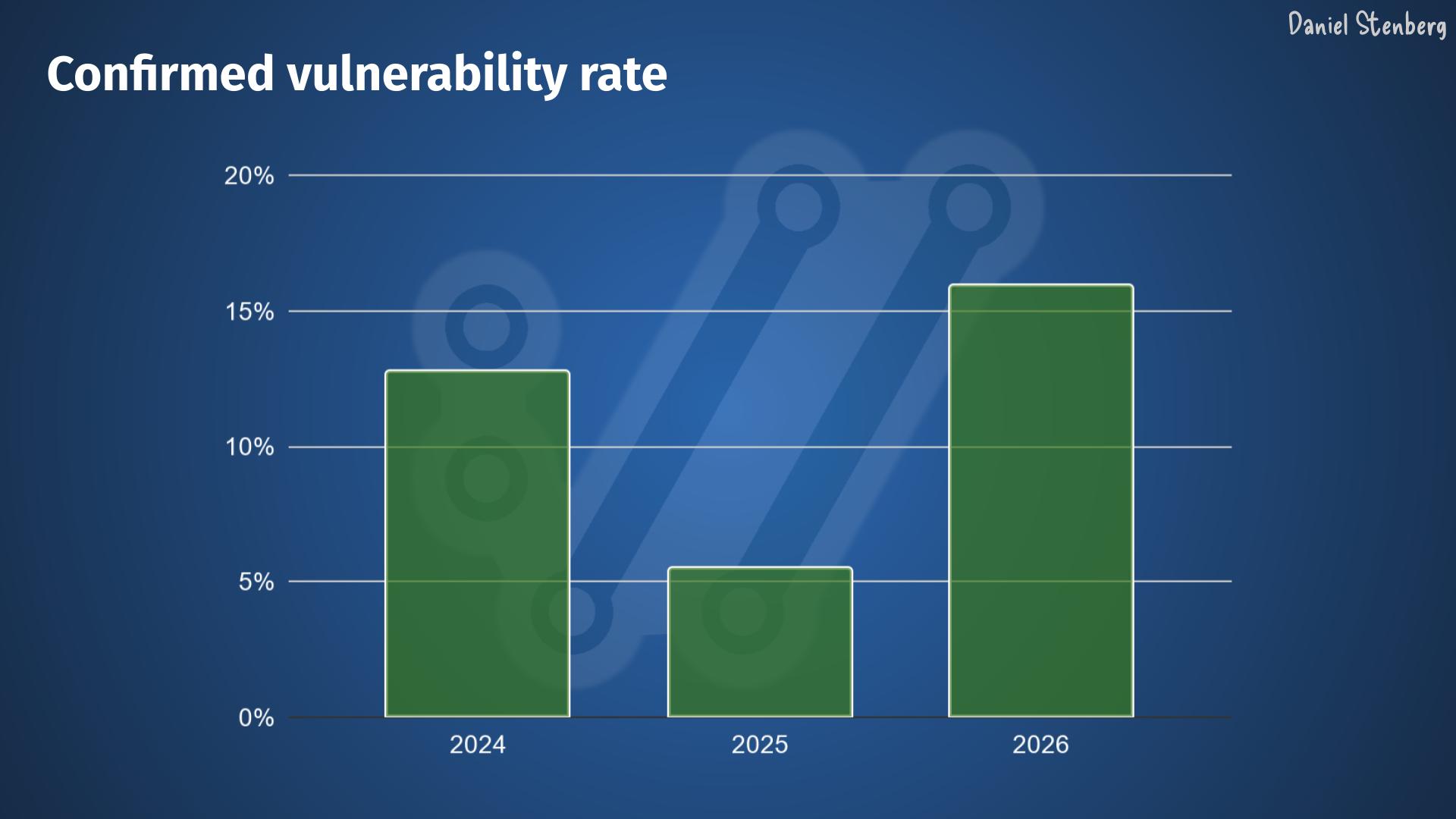
The quality is higher. The rate of confirmed vulnerabilities is back to and even surpassing the 2024 pre-AI level, meaning somewhere in the 15-16% range.
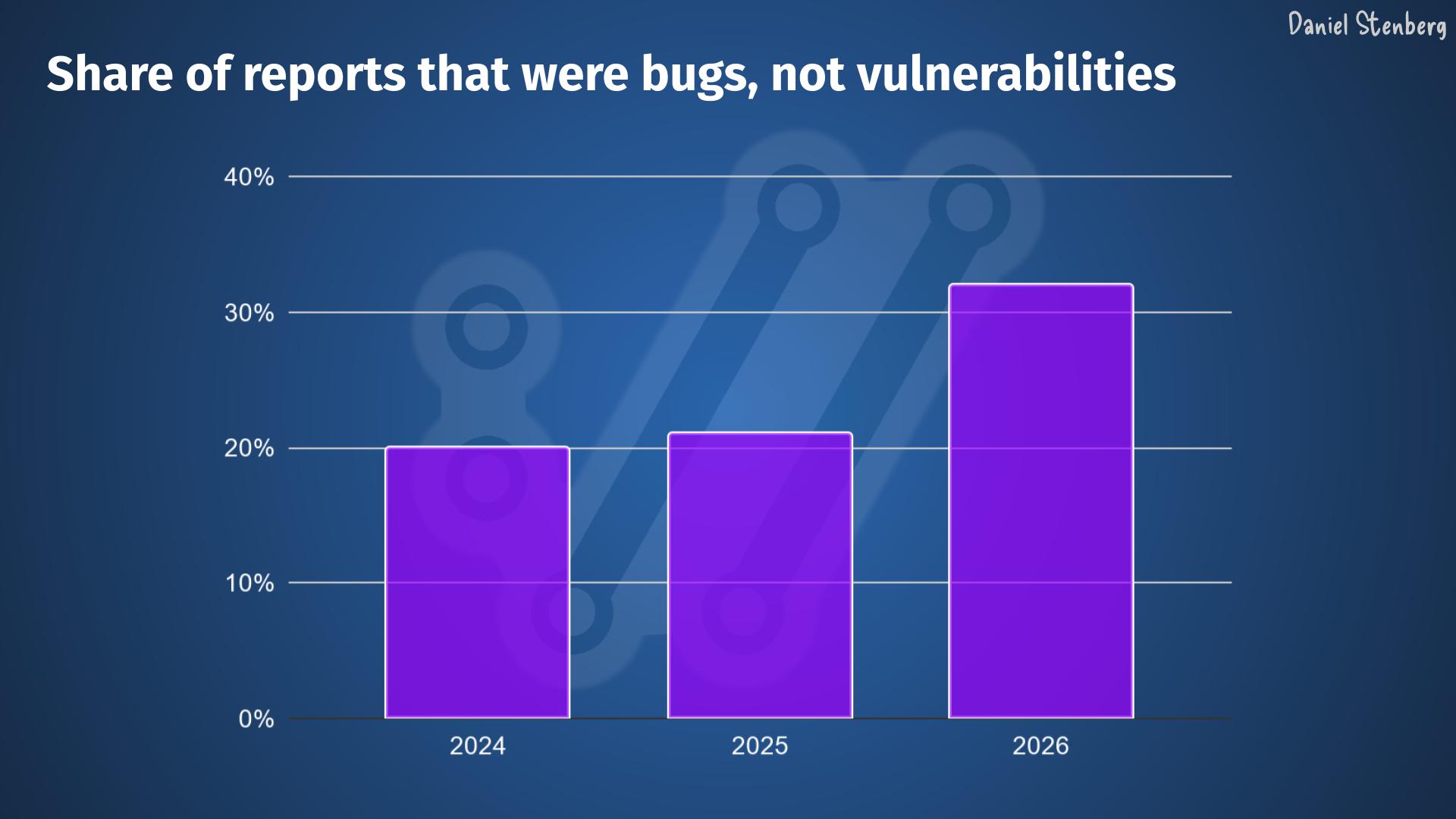
In addition to that, the share of reports that identify a bug, meaning that they aren’t vulnerabilities but still some kind of problem, is significantly higher than before.
Everything is AI now
Almost every security report now uses AI to various degrees. You can tell by the way they are worded, how the report is phrased and also by the fact that they now easily get very detailed duplicates in ways that can’t be done had they been written by humans.
The difference now compared to before however, is that they are mostly very high quality.
The reporters rarely mention exactly which AI tool or model they used (and really, we don’t care), but the evidence is strong that they used such help.
We are not unique
I did a quick unscientific poll on Mastodon to see if other Open Source projects see the same trends and man, do they! Friends from the following projects confirmed that they too see this trend. Of course the exact numbers and volumes vary, but it shows its not unique to any specific project.
Apache httpd, BIND, curl, Django, Elasticsearch Python client, Firefox, git, glibc, GnuTLS, GStreamer, Haproxy, Immich, libssh, libtiff, Linux kernel, OpenLDAP, PowerDNS, python, Prometheus, Ruby, Sequoia PGP, strongSwan, Temporal, Unbound, urllib3, Vikunja, Wireshark, wolfSSL, …
I bet this list of projects is just a random selection that just happened to see my question. You will find many more experiencing and confirming this reality view.
An explosion
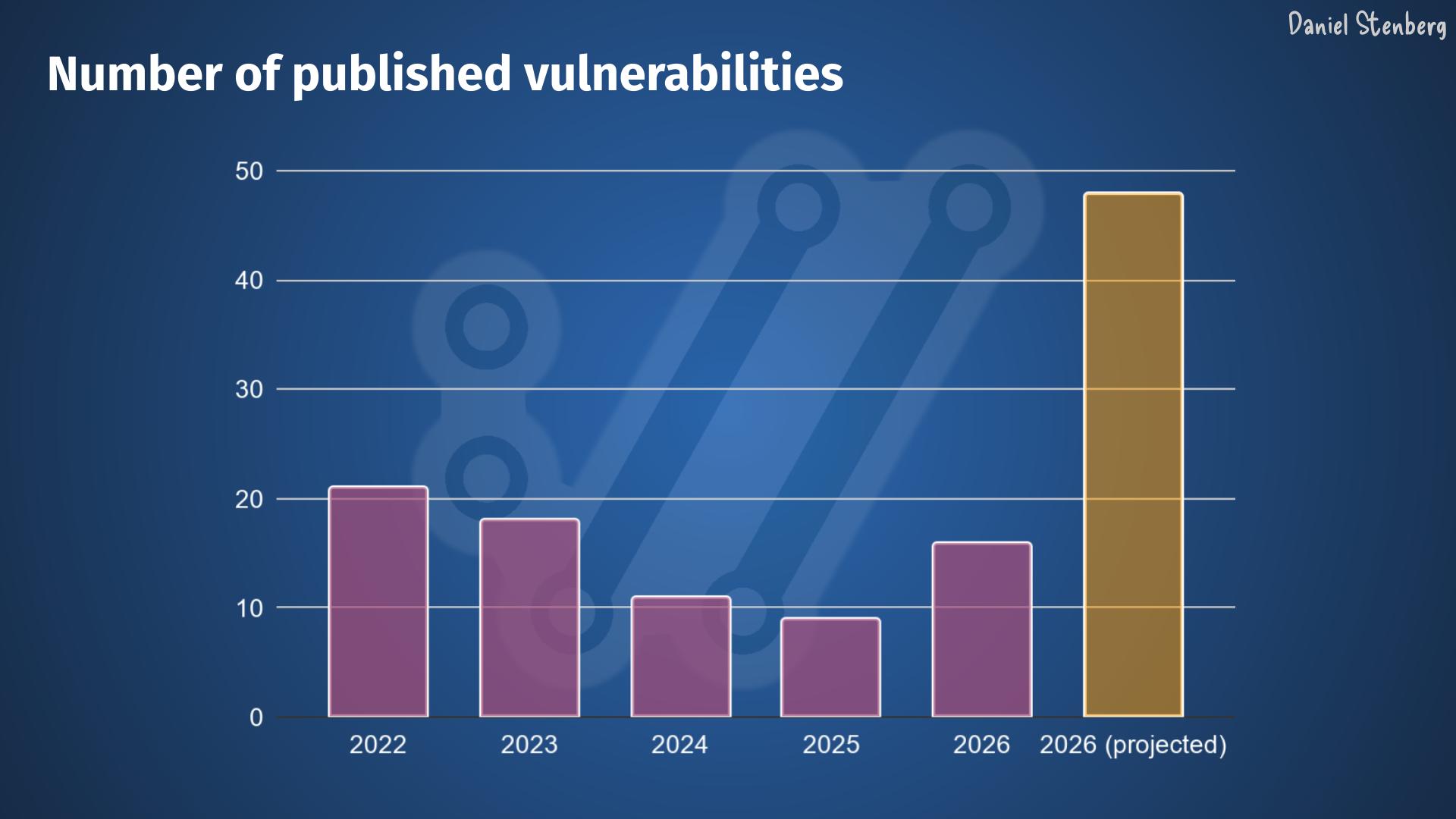
When we ship curl 8.20.0 in the middle of next week – end of April 2026, we expect to announce at least six new vulnerabilities. Assuming that the trend keeps up for at least the rest of the year, and I think that is a fair assumption, we are looking at an estimated explosion and a record amount of CVEs to be published by the curl project this year.
We might publish closer to 50 curl vulnerabilities in 2026.
Given this universal trend, I cannot see how this pattern can not also be spotted and expected to happen in many other projects as well.
Where does it end?
The tools are still improving. We keep adding flaws when we do bugfixes and add new features.
Someone has suggested it might work as with fuzzing, that we will see a plateau within a few years. I suppose we just have to see how it goes.
This avalanche is going to make maintainer overload even worse. Some projects will have a hard time to handle this kind of backlog expansion without any added maintainers to help.
It is probably a good time for the bad guys who can easily find this many problems themselves by just using the same tools, before all the projects get time, manpower and energy to fix them.
Then everyone needs to update to the newly released fixed versions of all packages, which we know is likely to take an even longer time.
We are up for a bumpy ride.


Well written Daniel.
Mozilla recently published their findings after having access to Mythos and it shows a similar trend.
They conclude with I believe a pretty positive note:
——-
Encouragingly, we also haven’t seen any bugs that couldn’t have been found by an elite human researcher. Some commentators predict that future AI models will unearth entirely new forms of vulnerabilities that defy our current comprehension, but we don’t think so. Software like Firefox is designed in a modular way for humans to be able to reason about its correctness. It is complex, but not arbitrarily complex.
The defects are finite, and we are entering a world where we can finally find them all.
——-
Link:
https://blog.mozilla.org/en/privacy-security/ai-security-zero-day-vulnerabilities/
“The defects are finite, and we are entering a world where we can finally find them all.” Nice thought, but as long as we develop software we introduce new bugs.
The high number of bugs show us, that the quality of our software wasn’t as good as we thought. And in addition we have to reduce complexity and should not change existing code without need nor roll out needles features. Mozilla is an example how it should not be in the future.
” as long as we develop software we introduce new bugs.”
Well, maybe, yes, no?
Mozilla just nulled 271 defects. The point being that these bugs where never “introduced”. They would have been introduced in Firefox 150, but they weren’t.
Sure they were introduced how else could they have been fixed? They were added in the past and now a tool found them and the developers fixed them.
My point is rather that developers will add new bugs as well going forward.
I think the argument is, that new bugs won’t get introduced, as you can run the AI checks before the release – so yes, technically the bugs got created, but also catched, before the code went productive.
@Name: that assumes we can find all newly created problems ourselves, which would be something never previously accomplished.
Hi Daniel,
what we’re currently seeing in haproxy is that we now have an opportunity for finding issues before security researchers and before attackers. By investing more time early fixing low-importance bugs, we expect to save time in the future not having to rush stable releases, dealing with CVEs nor arguing with reporters about whether a reported bug constitutes a vulnerability or not.
My feeling is that we’re currently dealing with a long backlog. Some bugs that were reported have been there for 10+ years, and who knows how long they could remain harmless before a combination with a new feature could turn them into exploitable vulnerabilities? Who knows how many of them were already spotted by attackers silently waiting for these to become exploitable? So we’re flushing a long tail of old, non-important bugs and that’s a great thing.
Another point is that by having developers getting used to seeing their patches questioned, we’ll further increase our coding standards. We noticed that these tools read comments and find inconsistencies between what comments say and what is done, and it turns out that we’ve always had the reputation of being abundant in comments (about 1/3 of the lines of code I think). So this indeed helps, and is a great opportunity for developers to continue to say “what comes here is safe for this or that reason”, which AI tools then challenge.
I do expect that we’ll issue more maintenance versions for a few weeks/months and that we might get less bug reports in the future and have to emit less maintenance versions than before, which is a good thing for us (more time spent developing features than fixing bugs), for users (less bugs and less upgrades) and the ecosystem as a whole (reduced attack surface).
We’ll see, but I find these times particularly interesting, even if quite exhausting 🙂
Interesting take. The part that stands out to me is that the noise problem has shifted from obvious slop to higher-quality, more actionable reports. That is a better problem than useless volume, but it still sounds like a serious maintainer-load issue if the volume keeps rising faster than teams can triage and fix it.